Consensus algorithms are a fundamental and indispensable component of a Blockchain network. The peers of a blockchain network utilize these mechanisms to reach a common agreement on the present state of the distributed ledger and, hence, the name Consensus Algorithms.
Besides, these algorithms bring a lot of other advantages such as participant commitment verification, leader designation, and data synchronization.
The consensus algorithms proffer security and reliability to a blockchain, the two principal features of the network.
They weed out fraudulent and insincere participants from the network by verifying their commitment in terms of energy or finances. They also designate the nodes responsible to add the following block of transactions to the chain and help maintain blockchains efficiently.
Although, this does not mean that all is well with these consensus procedures. They have their own set of trade-offs such as allowing centralization, high power consumption, and inequality.
There are various kinds of consensus algorithms such as Proof of Work, Proof of Stake, Practical Byzantine Fault Tolerance (PBFT), Proof of Burn, etc.
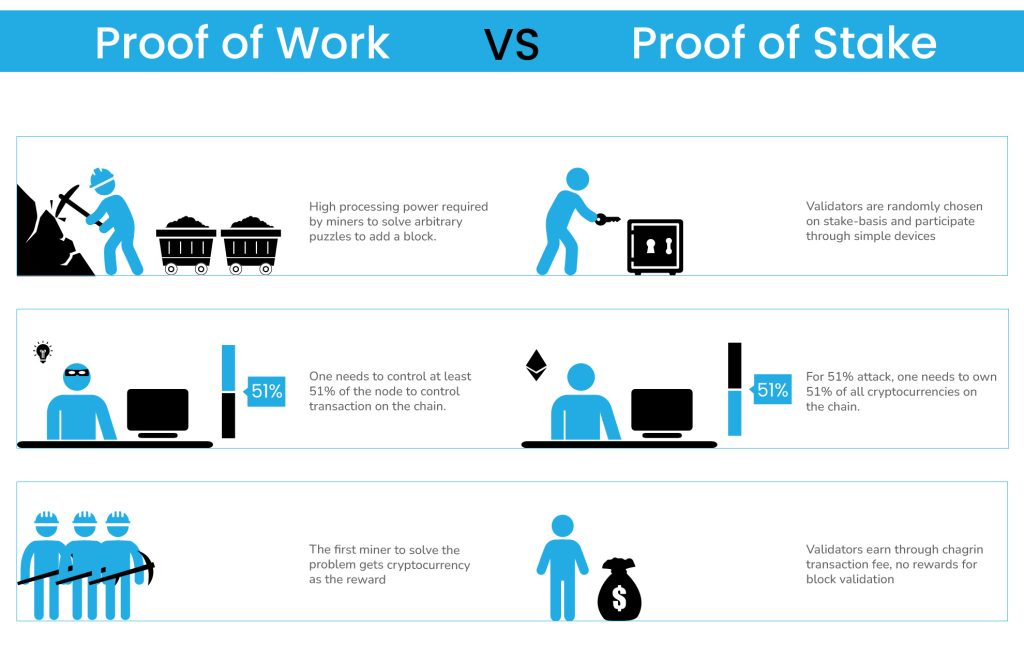
In this article, we will discuss two of the most popular consensus algorithms, Proof of Stake (PoS) and Proof of Work (PoW), and see why big platforms, like Ethereum, are shifting to the PoS algorithm from PoW.
We will see how PoS offers better safety, reliability, efficiency, and speed but most importantly, how it solves two of the main issues that mar Proof of Work, i.e. high power consumption and centralization.
What is Proof of Stake (PoS)?
The Proof of Stake mechanism works on the economic stake of the validators on the network. Hence, first, validators have to invest in the blockchain’s base cryptocurrency. Then, they have to lock some of their currency in the form of stakes. Once the stakes are placed, the process of proposing and voting for the next block starts.
Validators compute and propose a block they deem canonical and fit as the next block in the chain as per their calculation. Then the block that meets all the guidelines gets added to the chain and the validators of the block get rewarded.
There are various forms of PoS in which the rewards are assigned to the validators. However, two of the major ones are discussed below.
- Chain-based Proof of Stake – In this algorithm, a validator is chosen pseudo-randomly during each time slot. The validator has the right to create a block that mandatorily points to a previous block to make a single growing chain.
- BFT-style Proof of Stake – Here, BFT stands for Byzantine Fault Tolerance. In this flavor of PoS, validators have randomly conferred the right to propose blocks. However, the consensus on the valid block is achieved through a multi-round process. In this process, validators vote for a specific block in each round and ultimately agree on whether a given block is valid and should be part of the chain. Notably, the weight of each validator’s vote corresponds to the size of its stake.
The PoS is a wonderful alternative to existing algorithms and incentivizes validators for achieving consensus. It offers significant advantages such as security, reduced risk of centralization, and energy efficiency. Let’s discuss the advantages in detail.
Advantages of Proof of Stake
- Energy Efficient
According to the Cambridge Center for Alternative Finance (CCAF), Bitcoin (which follows PoW) consumes around 110 Terawatt Hours per year which is almost equal to the energy consumption by Sweden. The questions are being raised about high energy consumption by blockchain especially those that utilize PoW.
However, PoS is much more energy-efficient and utilize a fraction of the energy required by other algorithms. This is because it does not require heavy machinery to solve complicated puzzles like in the case of PoW. More on this in the later section.
- Maintaining Rarity
Since PoS make validation and mining easy on resource consumption, it does not necessitate a high rewarding system to encourage continuous participation by the validators. Moreover, it also creates room for lowering the reward over time to reduce the supply of the cryptocurrency.
- Discourage Centralization
PoS facilitate the utilization of mathematical models for egalitarian operations and discourages centralization of the system. It prevents the formation of cartels, in a rare event that they still form, it prevents them from acting in harmful ways.
It also reduces centralization risks by offering linear scalability and polish off any disproportionate advantages like better affordability of mass-production equipment like in PoW.
- Leave 51% Attack Needless
PoS has the ability to impose economic penalties for various forms of 51% attacks. It makes such attacks much more expensive than PoW, thereby, removing or reducing any form of gains that attackers assume.
What is Proof of Work (PoW)?
The Proof-of-Work consensus algorithm requires the network participants or miners to compete against each other. They have to solve highly difficult puzzles requiring extremely complex computation.
The first one to solve the puzzle gains the right to create and broadcast a new block over the network. Then, the other nodes audit the block individually and if the block conforms to all the standards and guidelines, it is added to the existing blockchain. The creator or block is rewarded with cryptocurrencies for utilizing its resources, in this case, electrical energy.
The process is called mining and the participants are called miners. The reason is that the energy and the resources required to complete the process can be regarded as digital equivalent to mining for precious metals in the real-world.
Advantages of Proof of Work
- Encourages Renewable Energy
The high energy consumption forces the participants to look for cheaper and efficient renewable resources of energy to reduce the high cost of production.
Moreover, PoW inherently rewards overall efficiency i.e. higher energy efficiency and better technological performance. Leading to a healthier competition in both the aspects.
This has even led to a search of trapped energy and harness it for mining. - Higher Security
This mechanism requires a higher initial hardware cost and recurring resources expenditure, thus, it is difficult and costly to attack. This can be compared to Proof-of-Stake where a single small upfront expense is enough to participate.
Proof of Stake vs Proof of Work: Pros & Cons
| Proof of Stake | Proof of Work | |
|---|---|---|
| Participants | They are called Validators as they primarily validate the block to add it to the blockchain by staking their cryptos. They are randomly chosen for the right to propose a block. | They are called Miners because they have to use huge resources to solve a puzzle and achieve the right to create and broadcast a block. |
| Resources Required | Validators should possess Coins or tokens to put as a stake. | The miner should be able to invest in high resources to participate. |
| Cost | Low Cost in terms of infrastructure. But miners have to invest in the base coin of the blockchain. | High cost of infrastructure required and recurring cost of energy resources. |
| Pros | – Low Cost of equipment – Energy efficient. – Higher Speed – High scalability – Discourages Centralization and 51% attack | – High cost of equipment to discourage attacks, thus, higher security. – Rewards efficient resources utilization such as energy, infrastructure and technology |
| Cons | – Comparatively new, not as proven in terms of security as proof of work. – Network Control can be purchased | – Enormous amount of energy required – High cost of participation – Prone to Centralization |
FAQs
Reaching consensus on distributed networks safely and efficiently is not easy as some nodes might fail to participate or act dishonestly. The only way to achieve consensus is by having at least two-third or more reliable and honest network nodes. Hence, a mechanism is put in place so that the system works even if all the node are not are not participating in the voting process.
Byzantine fault tolerance (BFT) is a systemic ability to resist the class of failures derived from the Byzantine Generals’ Problem i.e. agree on a common solution to have coordination, whether yes or no. There is no correct answer, what matters is that the answer of all the participating nodes should be the same. A BFT system continues to function successfully even if some of the nodes fail or act maliciously.
A 51% attack is a probable infringement on a blockchain network, where a single entity or organization possesses the majority of computational power and uses this power for network disruption. In such a scenario, they can
– Intentionally exclude or modify the ordering of transactions.
– Reverse transactions to cause a double-spending problem.
– Prevent some or all transactions from being confirmed
– Prevent some or all other miners from mining for mining monopoly
– Reverse transactions from other users
– Prevent transactions from being created and broadcasted to the network.
– Change the block’s reward,
– Counterfeit crypto coins
– Steal coins
No, Bitcoin utilizes Proof of Work wherein the miners direct their effort to solve a complex mathematical puzzle to validate transactions and, in return, earn bitcoins. Proof of work is widely used in mining cryptocurrency. The transactions are processed peer-to-peer in a secure manner without the need to trust a third party.